Blog
The Advantages of Managed Services for New and Growing SMBs
Technology is essential for running operations, being productive, and staying competitive. Understanding IT needs is critical for efficient business operations, managed IT offers a range of...
Risky Business? Not Anymore With This Cybersecurity Risk Assessment Guide
A cyber security risk assessment is a systematic process that identifies, analyzes, and evaluates potential security threats to an organization's information systems and data assets. For...
What Every Small Business Needs to Know About IT Solutions
Small business IT solutions encompass the technology services, tools, and support systems that keep your operations running smoothly while protecting against cyber threats. Here's what every...
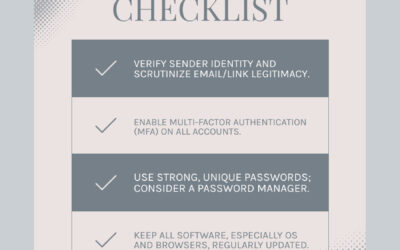
Protect Yourself Online – How to Stop Phishing Attacks
Understanding the Phishing Threat Learning how to prevent phishing attacks is vital. Phishing is a cyber-attack where scammers try to trick you into giving them your personal information or...
Encryption Explained: What is Data Encryption and Why Should You Care?
Data encryption is the process of converting readable information (plaintext) into scrambled, unreadable code (ciphertext) using mathematical algorithms and secret keys. Only authorized...
Network Security: Why Your Business Can’t Afford to Ignore It
Who needs network security? The simple answer is: everyone. Individuals and Families: To protect personal data, financial information, and smart home devices. Small Businesses and Startups:...
Hang Up on Bad Calls – The Ultimate Roundup of Business Phone Systems
Why Your Business Needs a Modern Phone System Phone systems for businesses have evolved far beyond simple voice calls. Today's solutions offer cost savings of 50-70% compared to traditional...
Stuck? Here’s How to Start Recovery Mode Easily
When your computer won't start or crashes unexpectedly, knowing how to start recovery can be the difference between a minor inconvenience and a major business disruption. Recovery mode is a special...
Hard Drive Heartbreak? Find Quick Data Recovery Services
When Your Hard Drive Fails: Finding Help Fast The sudden silence of a once-whirring hard drive, or the chilling error message that blocks access to years of family photos or mission-critical...
Watching the Wire: How to Monitor Network Traffic Effectively
Why Network Traffic Monitoring Is Critical for Business Security Learning how to monitor network traffic is essential for protecting your business from cyber threats and ensuring smooth...
Follow Stradiant